目录
- linux内核死锁调试
- 打开以下配置
- 测试code
- 总结
linux内核死锁调试
使用内核的kernel hacking功能
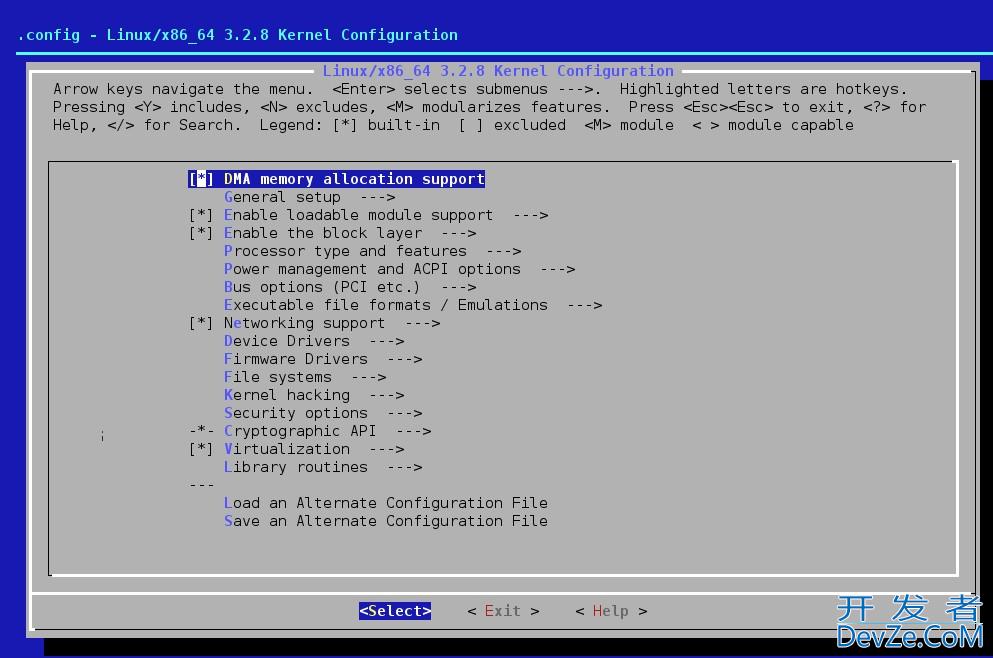
打开以下配置
CONFIG_PROVE_LOCKING=y CONFIG_LOCK_STAT=y CONFIG_DEBUG_LOCKDEP=y
重新编译内核后,
proc目录下会有lockdep lockdep_stats lockdep_chains说明lockdep模块已经生效
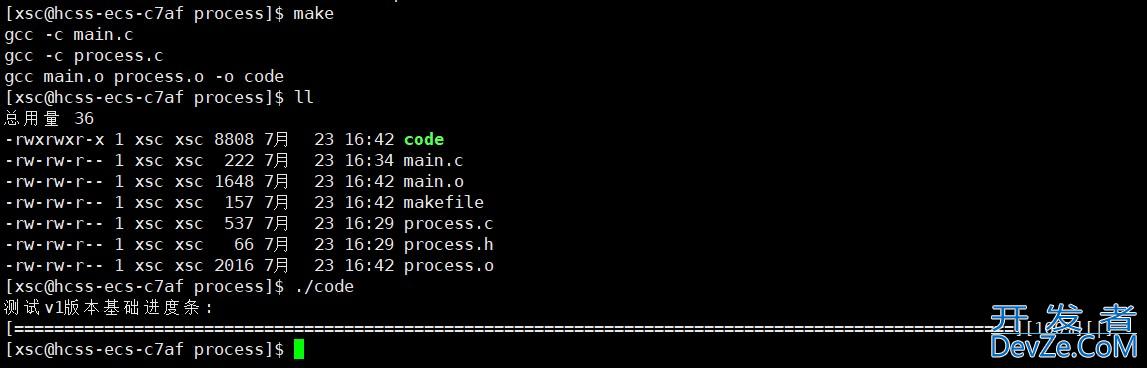
测试code
#include <linux/kernel.h>
#include <linux/module.h>
#include <linux/init.h>
#include <linux/slab.h>
static DEFINE_SPINLOCK(hack_spinA);
static DEFINE_SPINLOCK(hack_spinB);
#ifdef MEMORY_TEST
static char* buf;
static vophpid create_slue_err(void){
buf = kmalloc(32,GFP_KERNEL);
if(buf) {
/*memset(buf,0x00,33);*/
/* kfree(buf);
printk("%s\n","free buf" );*/
/*kfree(buf);*/
memset(buf,0x00,33);
}
return;
}
#endif
void hack_spinBA(void) {
printk("%s\n","hack_spin:B=>A\n" );
spin_lock(&hack_spinA);
spin_lock(&http://www.devze.comamp;hack_spinB);
}
void hack_spinandroidAB(void) {
printk("%s\n","hack_spin:A=>BFYpBRNn" );
spin_lock(&hack_spinB);
}
static int __init my_test_init(void) {
printk("init %s\n", "my_test_init 1");
#ifdef MEMORY_TEST
create_slue_err();
#endif
hack_spinBA();
编程客栈 hack_spinAB();
printk("init %s\n", "my_test_init 2");
return 0;
}
static void __exit my_test_exit(void) {
printk("%s\n","my_test_exit" );
return ;
}
MODULE_LICENSE("GPL");
module_init(my_test_init);
module_exit(my_test_exit);
测试打印:
[ 188.596504@1] init my_test_init 1
[ 188.596548@1] hack_spin:B=>A[ 188.596548@1] [ 188.598679@1] hack_spin:A=>B[ 188.598679@1] [ 189.920389@1] BUG: spinlock lockup suspected on CPU#1, insmod/6999[ 189.920943@1] lock: hack_spinB+0x0/0xfffffffffffffef4 [slub_test], .magic: dead4ead, .owner: insmod/6999, .owner_cpu: 1[ 189.931758@1] CPU: 1 PID: 6999 Comm: insmod Tainted: G O 3.14.29 #6[ 189.938784@1] Call trace:[ 189.941406@1] [<ffffffc0010893f8>] dump_backtrace+0x0/0x144[ 189.946896@1] [<ffffffc001089558>] show_stack+0x1c/0x28[ 189.952120@1] [<ffffffc001b5b480>] dump_stack+0x74/0xb8[ 189.957247@1] [<ffffffc0010fb6d4>] spin_dump+0x78/0x98[ 189.962369@1] [<ffffffc0010fb904>] do_raw_spin_lock+0x170/0x1a8[ 189.968199@1] [<ffffffc001b670a8>] _raw_spin_lock+0x68/0x88[ 189.973764@1] [<ffffffbffc00507c>] hack_spinAB+0x30/0x3c [slub_test][ 189.980015@1] [<ffffffbffc00d028>] $x+0x28/0x4c [slub_test][ 189.985566@1] [<ffffffc0010816d4>] do_one_initcall+0xd4/0x13c[ 189.991257@1] [<ffffffc00112c2f8>] load_module+0x16d8/0x1e08[ 189.996834@1] [<ffffffc00112cba0>] SyS_finit_module+0x80/0x90[ 211.641019@1] INFO: rcu_sched detected stalls on CPUs/tasks: { 1} (detected by 2, t=2104 jiffies, g=18446744073709551337, c=18446744073709551336, q=4)
[ 211.648804@2] Task dump for CPU 1:[ 211.652167@2] insmod R running task 0 6999 5821 0x0000000a[ 211.659325@2] Call trace:[ 211.661920@2] [<ffffffc001085f10>] __switch_to+0x74/0x8c
很明显可以看出死锁的发生路径与调用栈
hack_spinAB在申请spin_lock(&hack_spinB)时死锁了
总结
以上为个人经验,希望能给大家一个参考,也希望大家多多支持编程客栈(www.devze.com)。

 加载中,请稍侯......
加载中,请稍侯......
精彩评论